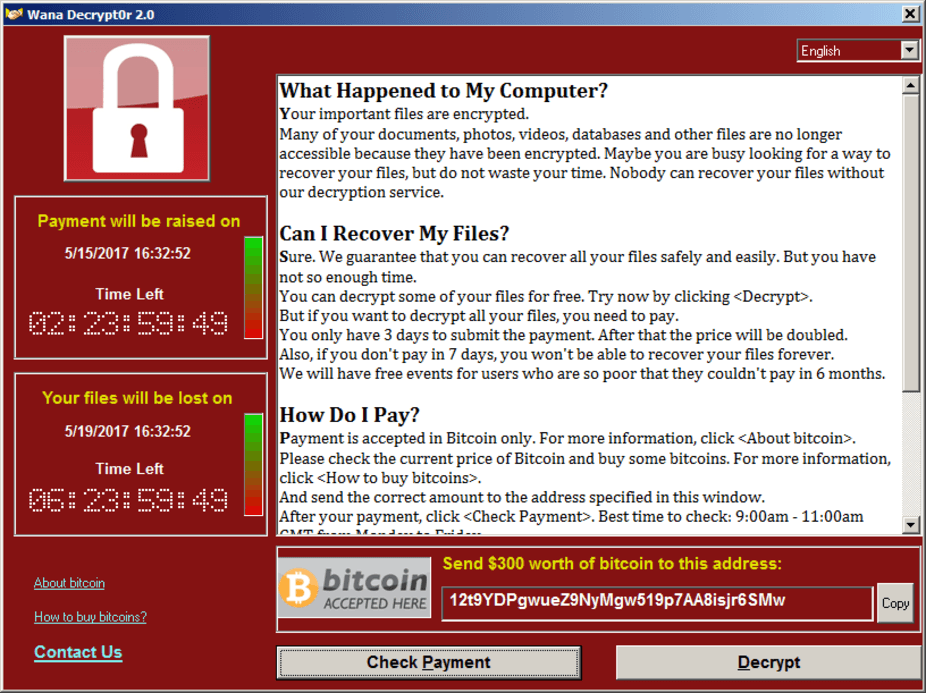
A massive malware attack was launched on Friday, affecting at least 75,000 computers in 99 countries. Computers running Microsoft Windows were infected with “WanaCrypt0r 2.0 or WannaCry” ransomware. Once infected, all of the files on the computer are encrypted by the malware, which then displays a ransom demand of between US $300 and $600 in bitcoin that needs to be paid before the files can be decrypted.
The WannaCry ransomware is being spread through a weakness in Microsoft Windows that was originally exploited by the US National Security Agency (NSA) as part of their arsenal of cyberweapons in a tool called “Eternal Blue”. Unfortunately, this tool, along with many others, was stolen by hackers and leaked to the world in April 2017 by a hacker group calling themselves the “Shadow Brokers”.
Microsoft had already released a fix for the Eternal Blue vulnerability in March, but the extent of the WannaCrypt attack has highlighted how many organisations have failed to apply the fix, or are running copies of Windows that are so old that there wasn’t a fix for them.
Russia, Ukraine and Taiwan have been the countries most affected by the attack. In the UK however, the attack hit the National Health Service badly enough that services to patients were disrupted.
At the time or writing, one of the bitcoin addresses used by the malware showed that only a few people had paid the ransomware so far but the number has been slowly ticking up.
The spread of the first wave of WannaCry ransomware may have been halted by a cybersecurity researcher who, by registering a domain with a particular name, effectively activated a “kill switch” in the malware software that stops it from spreading further.
Ransomware has become the biggest threat to organisations and governments trying to protect critical infrastructure. According to a study by IBM ransomware attacks increased by 6,000% in 2016 and at least 40% of spam emails now carry ransomware. The study also found that 70% of businesses infected with ransomware would pay the ransom. In many cases, this is because they either did not have backups, or they believed it was a faster way of getting their business back up and running.
The NHS has come in for particular criticism about the consequences of the attack because they new about the risks and had been warned repeatedly to take steps to protect their networks and computers.
Finding out who was behind the malware is going to be very difficult. The malware communicates using the anonymising Tor network and demands payments in the equally anonymous currency, bitcoin, making tracing those behind the attack more complicated.
The NSA has also been held partly to blame for the attack because it had not alerted Microsoft about the weakness in its system until the NSA’s software that exploited it had been stolen and leaked to the public. Had the NSA told Microsoft when it discovered the weakness, the patch to fix the vulnerability would have been available in enough time for even the slowest of organisations to have patched their computers.
Ironically, large scale attacks such as these do have the effect of highlighting the threat of malware attacks and cybersecurity in general. This is true at the national level as well as amongst businesses. The frequency and scale of attacks also gives us a measure of how effectively companies and countries are prepared for cybersecurity attacks of any kind. Governments can act to enforce cybersecurity protective measures on companies, especially those that provide critical services or infrastructure. They can also act to direct their security services to disclose weaknesses in software systems, rather than keeping them secret in order to exploit them themselves against some future enemy.
Companies and their employees can help protect themselves from future attacks of ransomware by taking the following steps:
- Back up computers. This doesn’t stop a computer from being attack but effectively renders it ineffective because it is easy to re-install the system from a backup should it become locked by ransomware.
- Don’t click on links in emails unless you are expecting the email to contain a link. If you don’t know, double check with the sender. Equally, if you open a document and it asks to run macros, just say no. Avoid putting people into this situation in the first place by not sending links unless you have agreed prior to sending the email.
- Always update systems and software with the latest security updates. Better still, set the system to automatically do this on your behalf.
- Use antivirus software to protect systems.
- If infected, disconnect the computer from the network so that other computers are not infected.




 Kuaishou Stock Jumps on Kling AI IPO Plans and $20 Billion Valuation
Kuaishou Stock Jumps on Kling AI IPO Plans and $20 Billion Valuation  Apple Explores Intel and Samsung Partnerships to Diversify Chip Supply Chain
Apple Explores Intel and Samsung Partnerships to Diversify Chip Supply Chain  BHP Attracts AI-Focused Investors as Copper Demand Surges
BHP Attracts AI-Focused Investors as Copper Demand Surges  Dell Stock Hits Record High After Trump Endorsement, AI Server Demand Fuels Rally
Dell Stock Hits Record High After Trump Endorsement, AI Server Demand Fuels Rally  Judge Delays SEC Settlement With Elon Musk Over Twitter Stock Disclosure Case
Judge Delays SEC Settlement With Elon Musk Over Twitter Stock Disclosure Case  Samsung Shares Slide as Labor Talks Intensify Ahead of Planned Strike
Samsung Shares Slide as Labor Talks Intensify Ahead of Planned Strike  Palantir Reports Record Growth, Raises 2026 Revenue Outlook Above Expectations
Palantir Reports Record Growth, Raises 2026 Revenue Outlook Above Expectations  Broadcom Eyes $35 Billion AI Chip Financing Deal With Apollo and Blackstone
Broadcom Eyes $35 Billion AI Chip Financing Deal With Apollo and Blackstone  Hua Hong Semiconductor Stock Surges to Multi-Year High Amid AI Boom
Hua Hong Semiconductor Stock Surges to Multi-Year High Amid AI Boom  Ibiden Stock Surges as AI Chip Demand Boosts Profit Outlook
Ibiden Stock Surges as AI Chip Demand Boosts Profit Outlook  U.S.-China AI Talks May Take Center Stage at Trump-Xi Summit
U.S.-China AI Talks May Take Center Stage at Trump-Xi Summit  Anthropic’s $1.5B AI Venture with Wall Street Firms Targets Private Equity Market
Anthropic’s $1.5B AI Venture with Wall Street Firms Targets Private Equity Market  Trump Invites Top CEOs Including Nvidia, Apple, Boeing to China Summit With Xi Jinping
Trump Invites Top CEOs Including Nvidia, Apple, Boeing to China Summit With Xi Jinping  Infineon Raises 2026 Outlook as AI Data Center Chip Demand Surges
Infineon Raises 2026 Outlook as AI Data Center Chip Demand Surges